Hackers
are Demanding Ransom and
It's Getting Worse
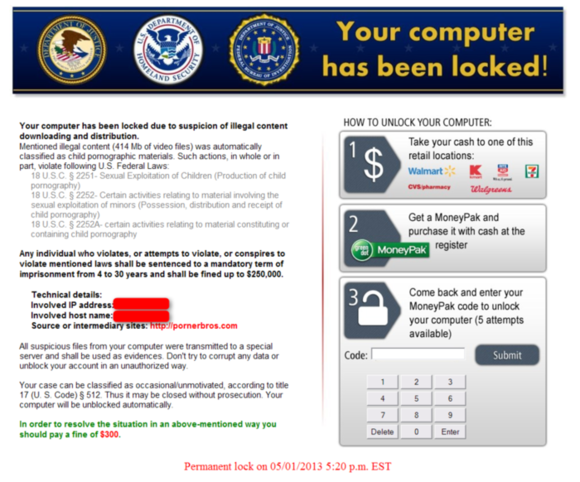
A class of malware attacks known as RansomWare is spreading and getting worse. You may have heard of (or experienced) cases where your computer displays a seemingly legitimate warning from the FBI or Homeland Security or such saying you committed some cyber bad stuff (visited the wrong website) and are guilty and being fined (a few hundred dollars), which you must pay before your computer is unlocked.
The earliest versions of this were relatively easy to remove, but they have been growing in sophistication. In addition, these types of infections have been getting through even updated antivirus programs. I presume that AV programs stop some of these, but since I have seen infected systems running almost every AV program, it is obvious that none are stopping all of them. I assume that there is some user failing as well which enables the infection to proceed, so it is not all the AV software's fault. Social Engineering has always been the biggest ace-in-the-hole of hackers.
Most of these attacks originate in Russia, China, and Eastern Europe, making it very difficult to track down and procescute the offenders.
Recently, there is a growth in a particularly nasty ransomeware which not only blocks your usage until you pay (and often does not release you even then), but which encrypts your entire hard drive or at least your data files (documents, pictures, music, etc.). If you pay, they say, you will be given the code to decrypt your files. Something called CryptoLocker and a variant call CryptoDefense have been around for several months and have struck at least 11,000 times in March 2014 alone, giving you a sense of the scope of this scourge.
These a--holes (I have nothing better to say and a whole lot worse) don't ask for large ransoms, a few hundred dollars. Therefore, many people say they would rather pay up and get their data back, than have to rebuild their entire system. However, do you trust that your system can be unlocked? They have your money and what can you do. Also, keeping the amount low keeps the FBI interest low as well. If they demanded millions, well, you know that money talks.
What can you do?
There are a few things you can do to minimize the risk, but, as I said earlier, nothing (so far) is perfect. Obviously, keep your AV up-to-date and practice "safe computing" (don't open email attachments that you are not expecting, don't visit dodgy web sites, keep you computer updated, etc).
One of the most important things is to maintain a good backup. If your computer is encrypted, that backup may the the only way to recover you stuff. If you keep your backup drive connected to you computer all of the time, it may be encrypted along with the rest, so backup drives should be disconnected when backup is not being run (difficult if the backup runs on a schedule, that's why I recommend that scheduling backup for individuals is not a good idea, and businesses should have a more robust backup system). Network shares (folders on other computers) can also be affected, so don't connect if it is not necessary.
If you do get hit, call or email me (610-395-5570 or ). I can evaluate how bad the damage is and what is necessary to recover what can be recovered.